Evolution of Cybersecurity Threats in the Crypto Space
In 2025, hackers have significantly evolved their operations, particularly in how they launder cryptocurrency after an exploit. According to a recent report by a leading blockchain analytics firm, the techniques used by cybercriminals have become more sophisticated, and the threats they pose to the crypto space are more severe than ever.
The report analyzed 255 reported incidents, resulting in a total loss of $4.4 billion. While some sources, such as CryptoGazet.com, estimated the total losses at $3.4 billion, there is a consistent pattern emerging: hackers are targeting Web3 features and exploiting the AI agent environment.
One of the most alarming findings is the speed at which hackers move funds after an exploit. The fastest movement was recorded at around two seconds, according to the report. Despite this rapid action, about 50% of the stolen funds remain unspent for months or even longer.
Rapid Fund Movement and Laundering Techniques
In 42% of cases, hackers turned to Tornado Cash for laundering. Overall, the speed of moving funds doubled in the second half of 2025. In 76% of cases, hackers managed to move, split, or partially launder funds before the exploit was even intercepted and reported.
Victims have also improved their response times, reducing their reaction time by more than half in the second half of the year. This has been attributed to faster freezing of funds and better cooperation with exchanges, which led to a slowdown in exploits during the latter part of 2025.
Despite the increased speed of fund movement, it still took hackers an average of 10.6 days to launder funds in H2, up from eight days in the first half of the year. The bad actors fragmented their haul, taking it into smaller chunks through more intermediaries and over a slightly longer time span.
Shift in Targeted Protocols
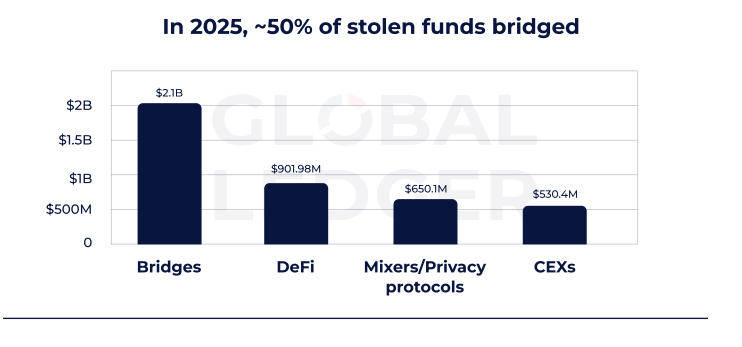
A notable shift occurred in the protocols targeted by hackers. Instead of relying on centralized exchanges for laundering, they increasingly tapped into the DeFi ecosystem. Over $732 million was laundered through DeFi in the second half of 2025, compared to $170 million in the first half. This represents a more than fourfold increase, making DeFi the second most-used laundering route after mixers.
This trend means that DeFi protocols are under significant pressure, as they directly connect to powerful laundering infrastructure.
Ethereum Remains the Top Target
Ethereum continues to be the primary target for attackers. It accounted for $2.44 billion in losses, or roughly 60% of the global total in 2025. Lex Fisun, CEO and co-founder of Global Ledger, highlighted that if you’re building on Ethereum with high liquidity, you’re the default target for hackers.
While other chains like Solana or Bitcoin are seeing an increase in incident counts, the majority of financial damage is still concentrated where the most liquidity exists.
Fisun emphasized that manual tracking of funds is not efficient enough to prevent losses. He suggested that the solution may lie in instant labeling of the source of funds and automated tracing of transactions.
Real-Time Monitoring and Security Measures
“To close the gap between a hack and response, DeFi protocols need real-time action. Here, implementing real-time on-chain monitoring that detects anomalies the moment they happen. Without internal detection and alerting, no ecosystem response can be fast enough,” Fisun commented.
Bridges also played a key role in hacks. Nearly half of stolen funds, or $2.01 billion, were laundered or routed through bridges, which is over three times the amount that went through mixers.
One of the reasons for this was to move funds to the Ethereum L1 chain, which is more liquid and accessible. Bridges continue to attract hackers due to their liquidity, as well as for chain-hopping and disguising origins.
If you’re reading this, you’re already ahead. Stay there with our newsletter.