The Moonwell DeFi Lending Protocol Exploit: A New Era of AI-Generated Code Vulnerabilities
The DeFi lending protocol Moonwell recently suffered a loss of $1.78 million due to an oracle pricing error, marking what is being described as one of the first major exploits directly linked to AI-generated Solidity code. This incident has raised significant concerns about the reliability and security of artificial intelligence in software development, especially within the fast-paced and high-stakes world of decentralized finance (DeFi).
Moonwell, a decentralized lending market operating on Base and Optimism, discovered a critical oracle configuration issue that affected its Coinbase Wrapped Ether (cbETH) Core Market on Base. This flaw led to cbETH being valued at approximately $1.12 per token instead of its actual market price near $2,200, resulting in a 2,000x undervaluation. This miscalculation triggered instant liquidations across the platform.
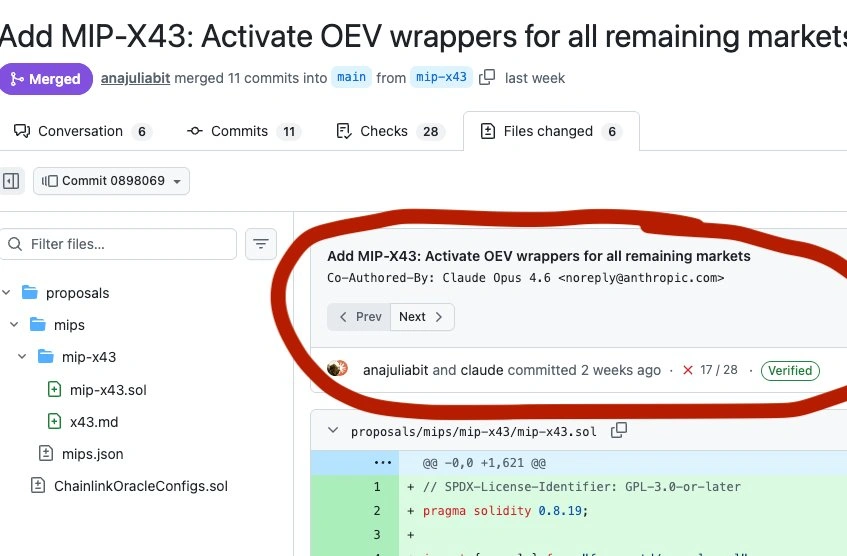
The vulnerability was traced back to code partially written by Anthropic’s Claude Opus 4.6 model. The code set the cbETH price at $1.12 instead of the correct value of $2,200. This error occurred just days after Moonwell activated governance proposal MIP-X43, which integrated Chainlink’s Oracle Extractable Value (OEV) wrapper contracts across Base and Optimism markets.
Instead of calculating the cbETH price in USD by multiplying the cbETH/ETH exchange rate by the ETH/USD price feed, the deployed code only obtained the cbETH/ETH exchange rate and treated that ratio as if it were already denominated in dollars. This fundamental mistake created a massive discrepancy in valuation, leading to widespread financial losses for users.
Impact on Users and the Protocol
With cbETH trading at lower prices due to Moonwell’s oracle, liquidators could repay around $1 worth of debt and get collateral worth thousands in return. This created an opportunity for malicious actors to exploit the system, borrowing more money than they should have been allowed to, thus increasing their debt within the protocol.
Moonwell’s risk manager was able to reduce the cbETH borrow cap to 0.01 within hours of the vulnerability, effectively freezing new borrowing activity and containing further damage. However, liquidations had already been processed, leaving users with catastrophic losses. The protocol estimated total losses at $1.78 million, primarily affecting cbETH, WETH, and USDC positions. Some borrowers nearly lost all their collateral, while others took advantage of the incorrect pricing to increase their debt.
Similar Incidents Highlight Systemic Risks
This incident is not unique. Just days earlier, the South Korean exchange Bithumb experienced a similar value assignment error. A staff member mistakenly entered “BTC” instead of “KRW” while distributing rewards for a Random Box promotion, resulting in users being rewarded in Bitcoin instead of Korean won. This error led to the project losing approximately 620,000 Bitcoin, worth over $40 billion—nearly 3% of Bitcoin’s entire global supply.
The Vibe Coding Debate Intensifies
The Moonwell incident has reignited the debate over “vibe coding,” where developers rely heavily on AI tools to generate code. Advocates argue that AI makes coding more accessible, while critics warn that its code may contain vulnerabilities that human reviews would likely miss.
Smart contract auditor Pashov emphasized that “behind the AI is a person who checks the finished work, and possibly an auditor. For this reason, blaming the neural network alone is incorrect, although the incident ‘raises concerns’ about vibe coding.”
Another blockchain security firm, SlowMist, shared its concerns about “oracle formula vulnerability” and the breakdown of human oversight that allowed the flawed code to reach production. A study published just weeks before the Moonwell incident identified 69 vulnerabilities across 15 applications created using popular AI coding tools, including Cursor, Claude Code, and Codes.
Even more concerning is that Anthropic’s own research from December 2025 revealed that Claude Opus 4.5 could exploit smart contract vulnerabilities worth $4.6 million by itself (in a simulated environment). The research also established that premier AI models can now “independently identify vulnerabilities, create working exploit chains, and extract value with minimal human oversight.”
Isolated Incident but Broader Implications
Despite the severity of the incident, Moonwell clarified that “no other markets on Base or OP Mainnet were affected. The issue is isolated to the cbETH Core Market on Base.” The protocol also noted that this was not its first oracle incident, recalling a misreporting incident in November 2025.
As the use of AI in software development continues to grow, the Moonwell incident serves as a stark reminder of the potential risks involved. While AI can offer efficiency and innovation, it also introduces new challenges that require careful oversight and rigorous testing to prevent future exploits.