Moonwell, a decentralized finance (DeFi) lending protocol built on Base and Optimism, suffered an exploit that resulted in approximately $1.78 million in losses. The incident was triggered by a mispricing in the Coinbase Wrapped Staked ETH (cbETH) oracle, which incorrectly returned a value of about $1.12 instead of the correct $2,200. This discrepancy allowed attackers to capitalize on the error, leading to significant financial damage.
In a post-mortem analysis, Moonwell revealed that a governance proposal executed on Sunday had misconfigured the cbETH oracle by relying solely on the cbETH/ETH exchange rate. As a result, the system reported cbETH at an incorrect price of around $1.12. Liquidation bots and opportunistic borrowers exploited this vulnerability, ultimately resulting in roughly $1.78 million in bad debt.
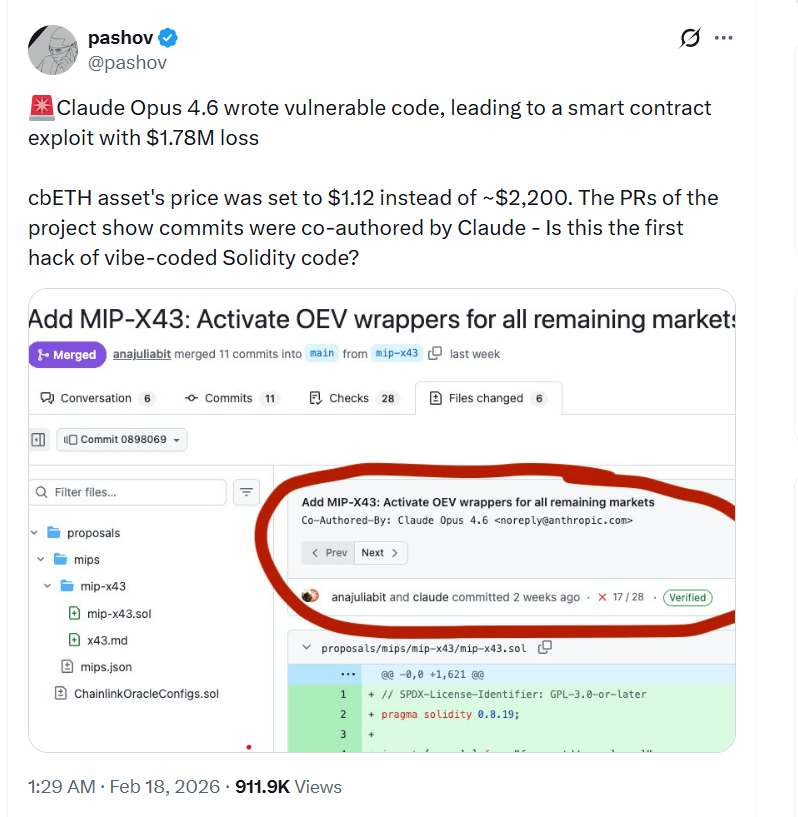
The affected contracts showed multiple commits co-authored by Anthropic’s Claude Opus 4.6, prompting security auditor Pashov to raise concerns about the potential role of AI in the development process. He highlighted the incident as an example of AI-assisted Solidity code causing unintended vulnerabilities.
Speaking to Cointelegraph, Pashov explained that he linked the case to Claude due to the presence of multiple commits in the pull requests that were co-authored by the AI model. He noted that “the developer was using Claude to write the code, and this has led to the vulnerability.” However, he cautioned against attributing the flaw solely to AI. Pashov emphasized that the oracle issue was the kind of mistake “even a senior Solidity developer could have made,” suggesting that the real problem lay in insufficient checks and end-to-end validation.
Initially, Pashov believed there had been no testing or audit at all, but later acknowledged that the team had conducted unit and integration tests in a separate pull request and had commissioned an audit from Halborn. In his view, the mispricing “could have been caught with an integration test, a proper one, integrating with the blockchain,” though he declined to directly criticize other security firms.
While the dollar amount of the exploit is relatively small compared to some of DeFi’s largest incidents—such as the Ronin bridge exploit in March 2022, where attackers stole over $600 million—Moonwell’s case stands out for its unique combination of factors. These include AI co-authorship, a seemingly basic pricing configuration failure on a major asset, and existing audits and tests that failed to detect the issue.
Pashov stated that his own company would not fundamentally change its processes, but if code appeared “vibe coded,” his team would “have a bit more wide open eyes” and expect a higher density of low-hanging issues, even though this particular oracle bug “was not that easy” to spot.
“Vibe coding” vs disciplined AI use
Fraser Edwards, co-founder and CEO of cheqd, a decentralized identity infrastructure provider, told Cointelegraph that the debate around vibe coding often obscures two distinct interpretations of how AI is used in development. On one side, he said, are non-technical founders who prompt AI to generate code they cannot independently review. On the other, experienced developers use AI to accelerate refactors, pattern exploration, and testing within a mature engineering process.
Edwards noted that AI-assisted development can be valuable, particularly at the MVP (minimal viable product) stage, but should not be treated as a shortcut to production-ready infrastructure, especially in capital-intensive systems like DeFi. He argued that all AI-generated smart contract code should be treated as untrusted input, subject to strict version control, clear code ownership, multi-person peer review, and advanced testing, especially around high-risk areas such as access controls, oracle and pricing logic, and upgrade mechanisms.
“Ultimately, responsible AI integration comes down to governance and discipline,” he said, emphasizing the need for clear review gates, separation between code generation and validation, and an assumption that any contract deployed in an adversarial environment may contain latent risk.
Related:
How South Korea is using AI to detect crypto market manipulation
Small loss, big governance questions
How AI crypto trading will make and break human roles
Magazine:
South Korea gets rich from crypto… North Korea gets weapons